My job involves lightweight pentesting and vulnerability assessment and such is the nature that clients know what I want to accomplish and will happily white-list any script I ask them to, but what’s the fun in that? Researching methods to bypass AV and thinking of methods to just not write to disk, showed that AV catches common scripts (Inveigh in this example) even when in memory and not on disk. I came across this article written by Black Hills Infosec that showed how easy AV evasion is and I thought that no way could this article written almost 2 years ago is still relevant.
I was wrong.
Particularly, I was trying to run Inveigh, which is the Windows version of Responder, but Windows Defender would constantly catch it. So I tried the methods in the Black Hills article.
I initially tried to just remove a line of code and rename the script, but that didn’t work.

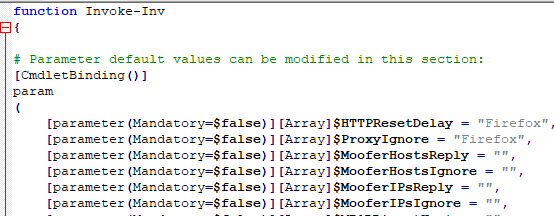
So instead, I took Inveigh.ps1 and renamed it to Inv.psm1

Next, I made three changes to the script via ctrl+F & replace.
- I removed the comment section
- I changed the word “Spoof” to “Moof”
- I changed the word “Inveigh” to “Inv”
And sure enough…

It turns out that AV evasion really isn’t difficult at all and even as quickly definitions of AV are updated, it takes almost no time to re-edit a script.

